analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
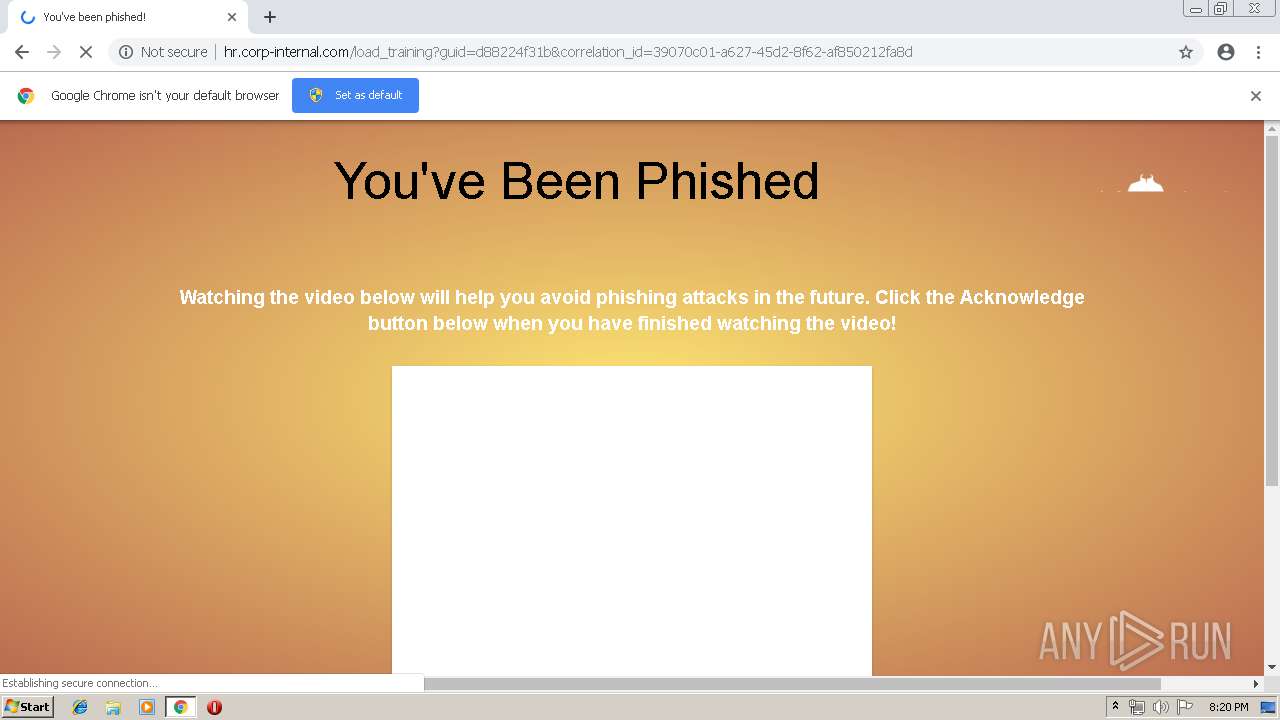
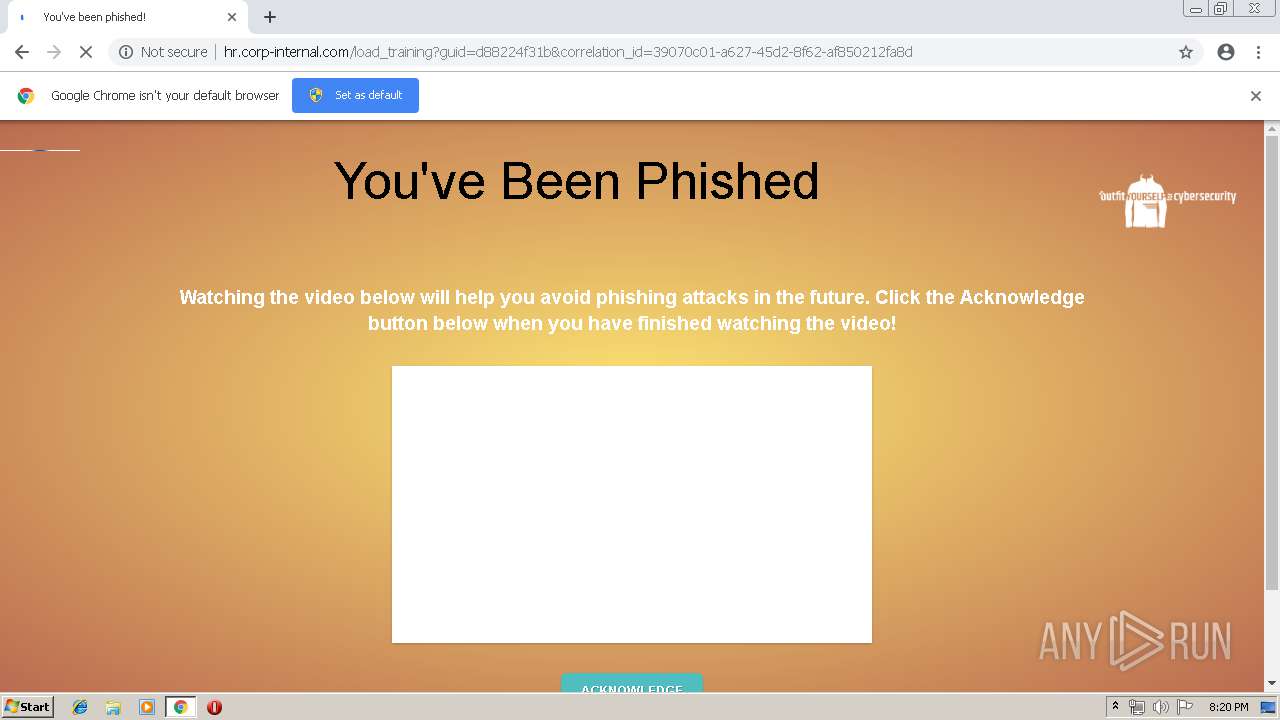
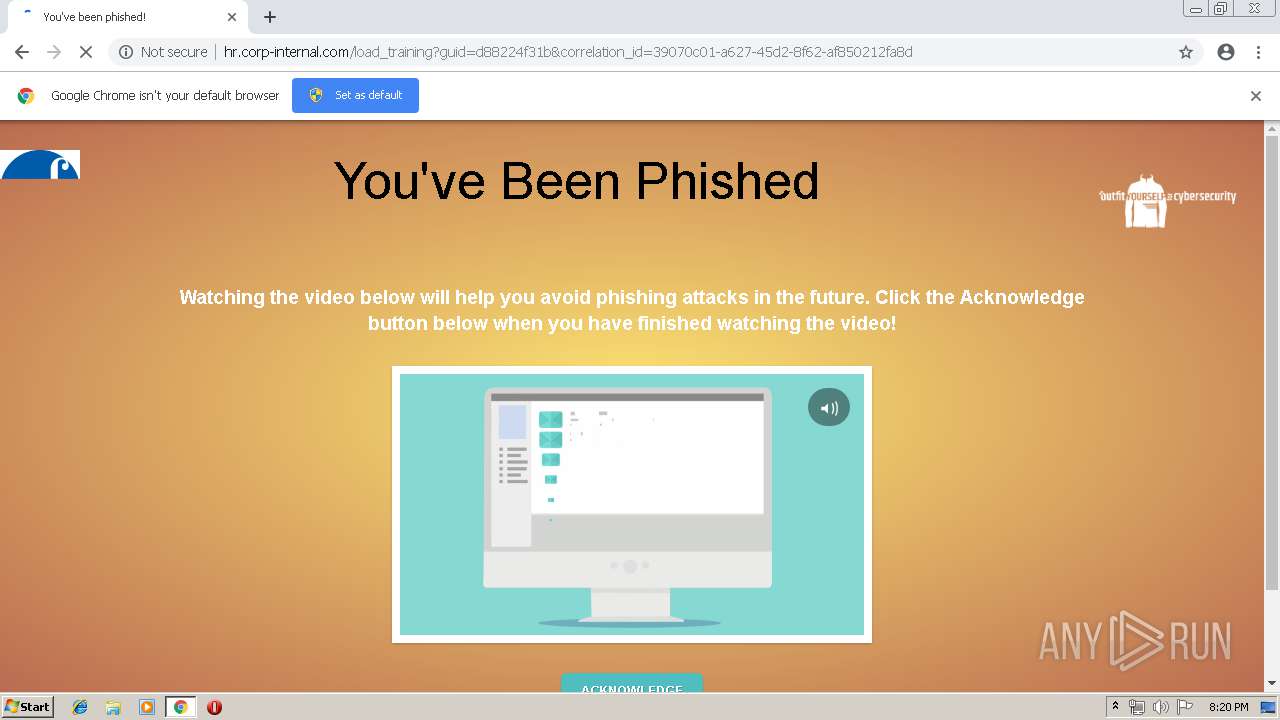
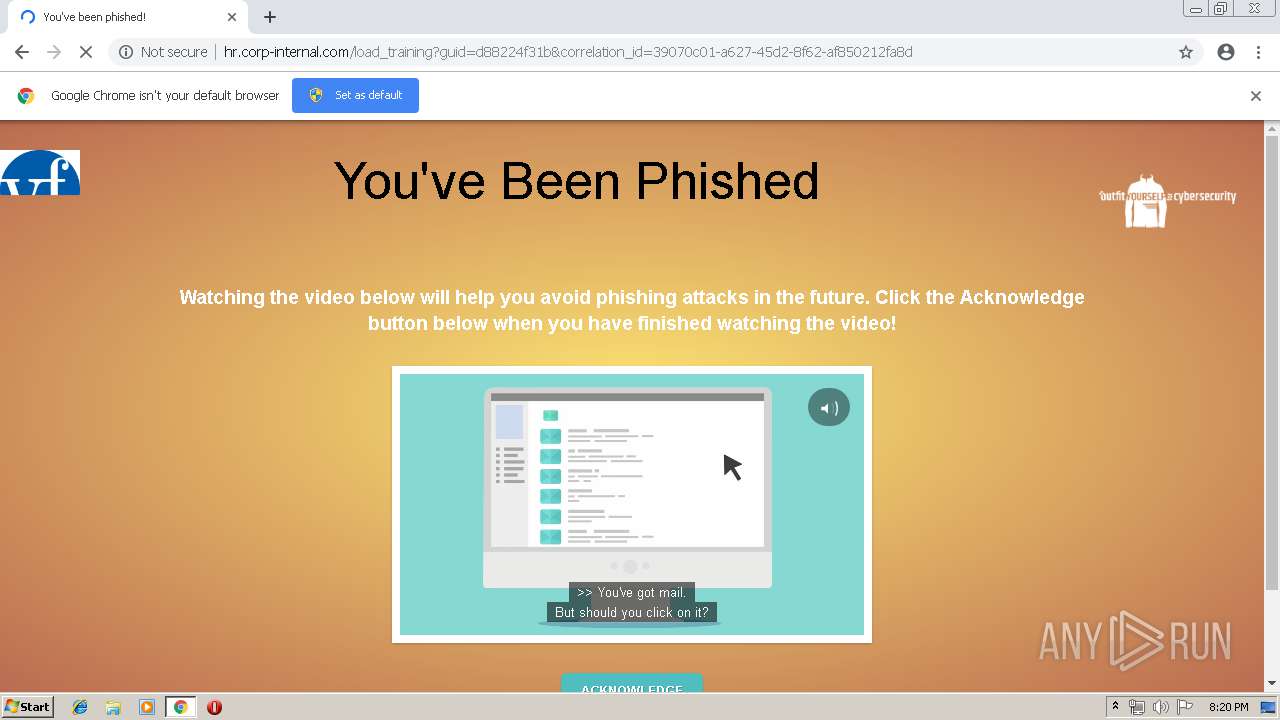
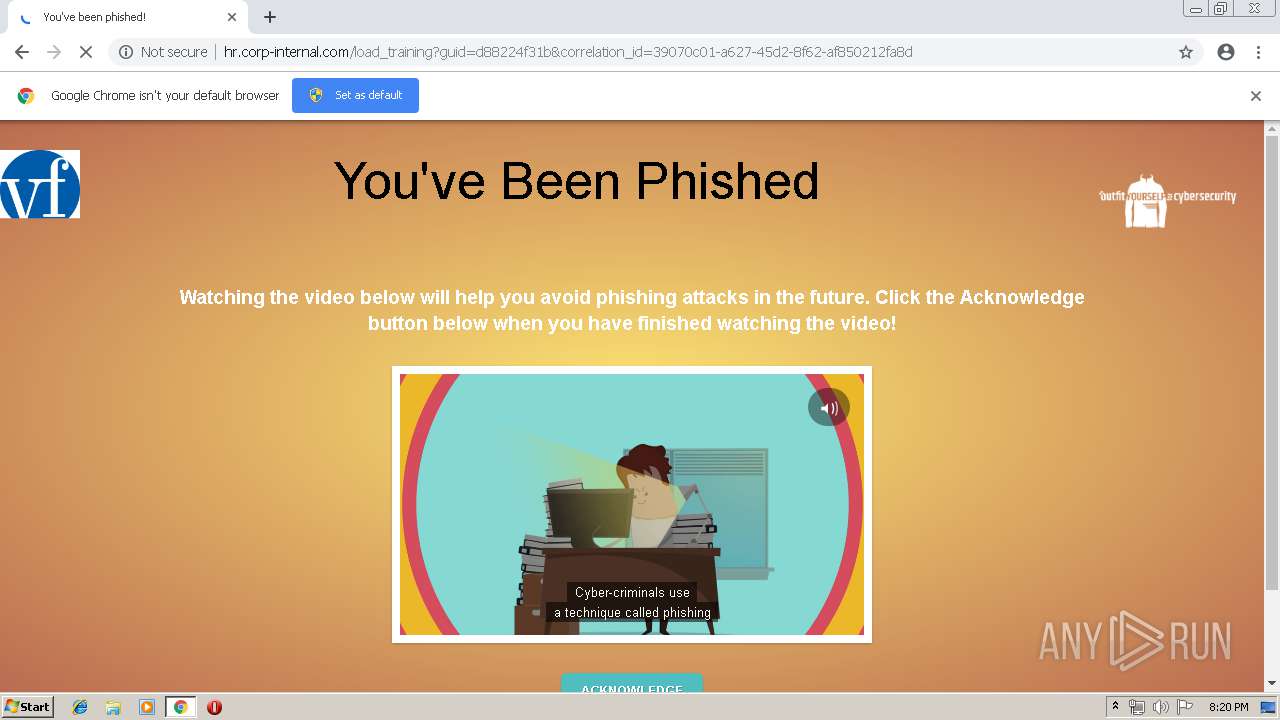
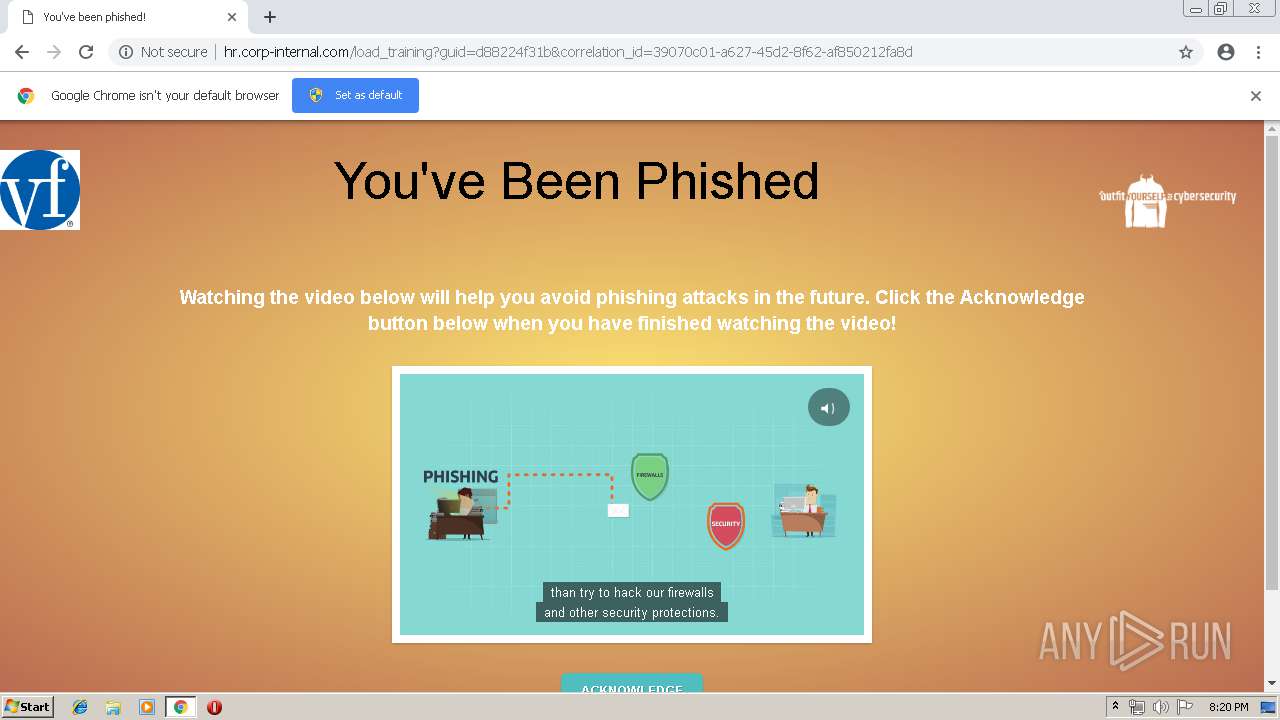
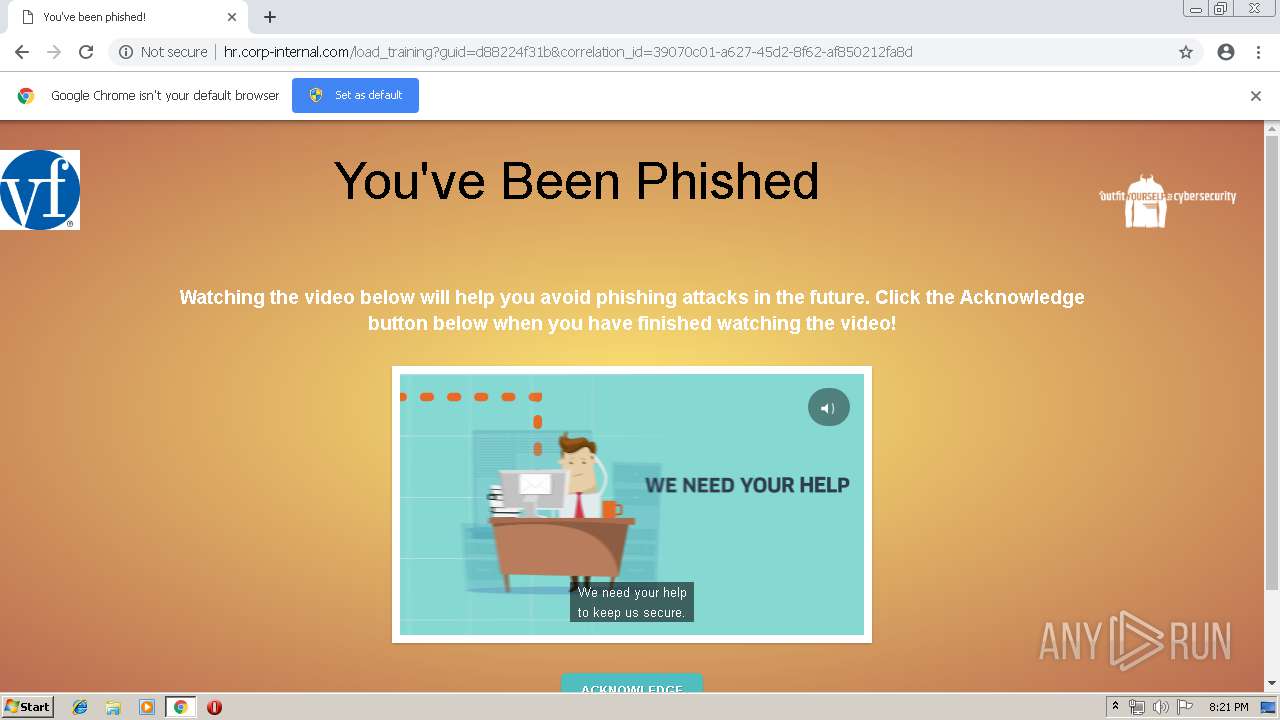
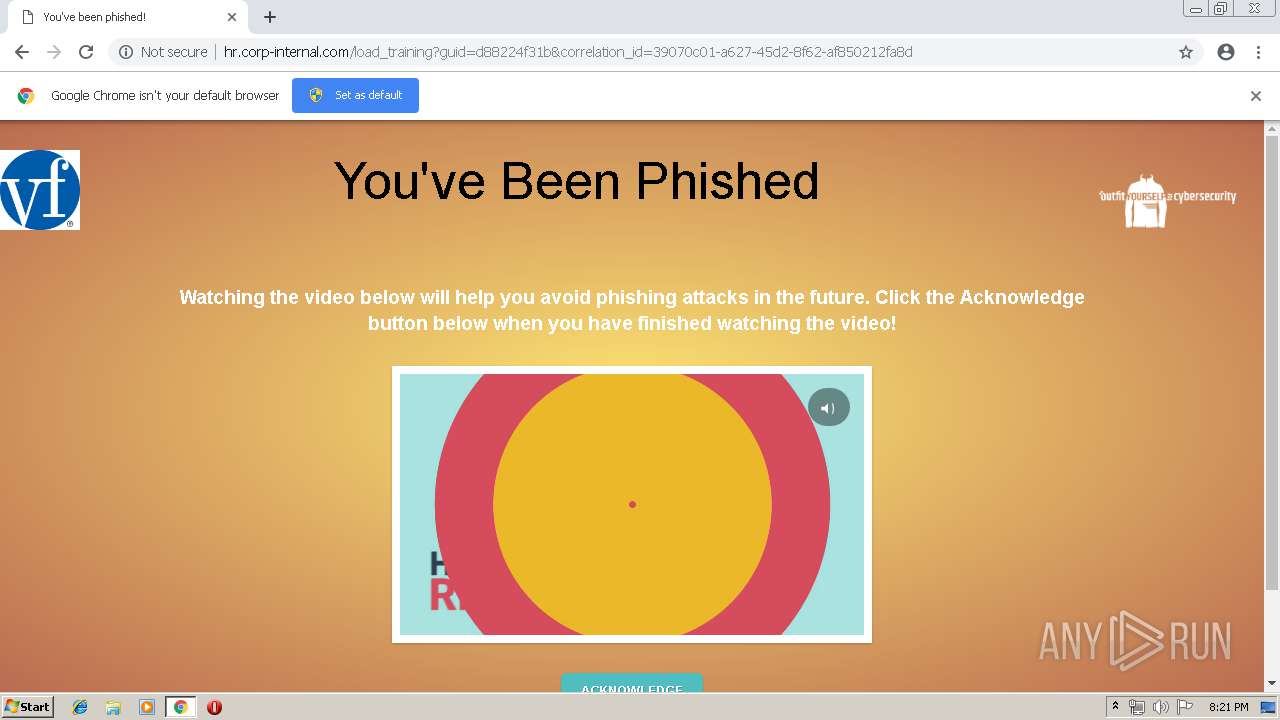
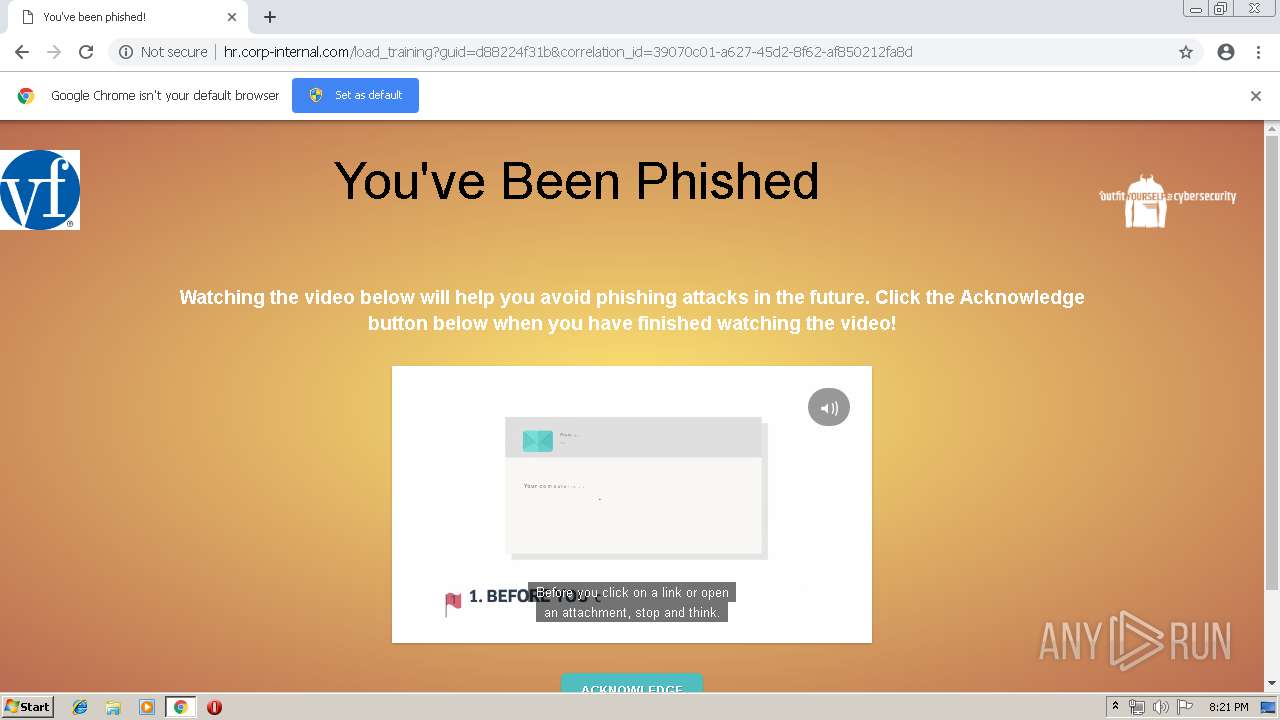
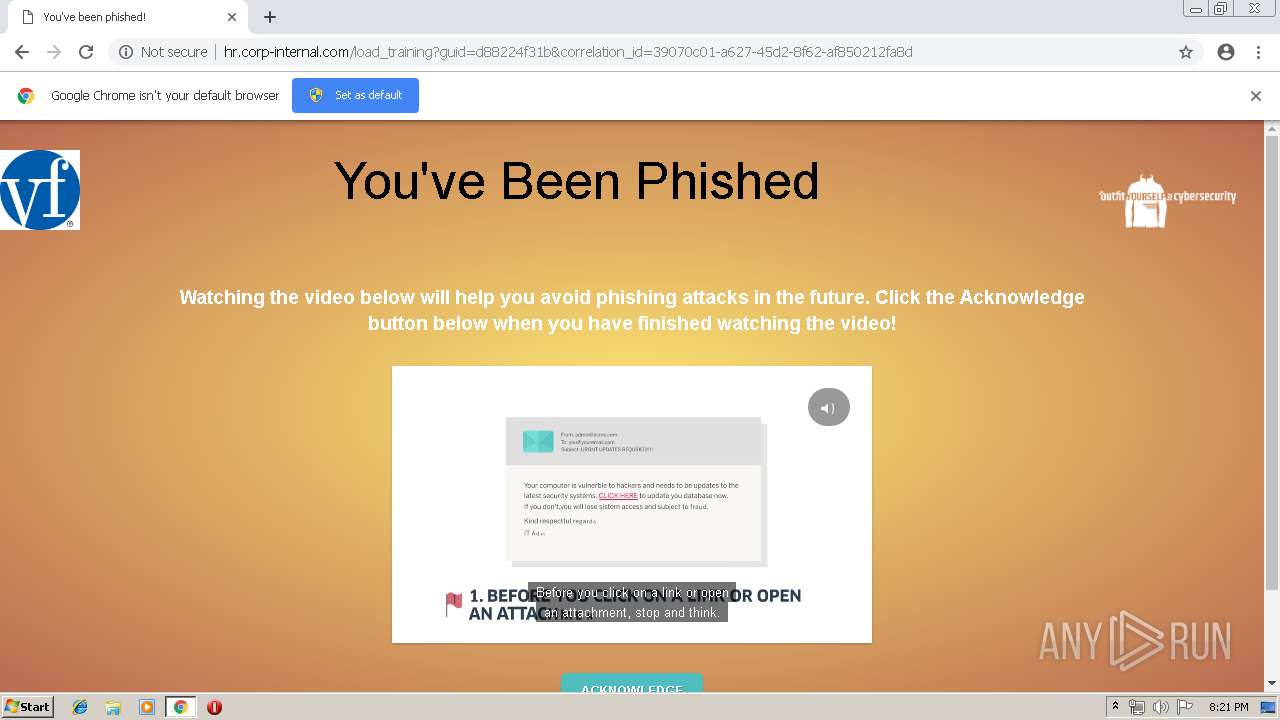
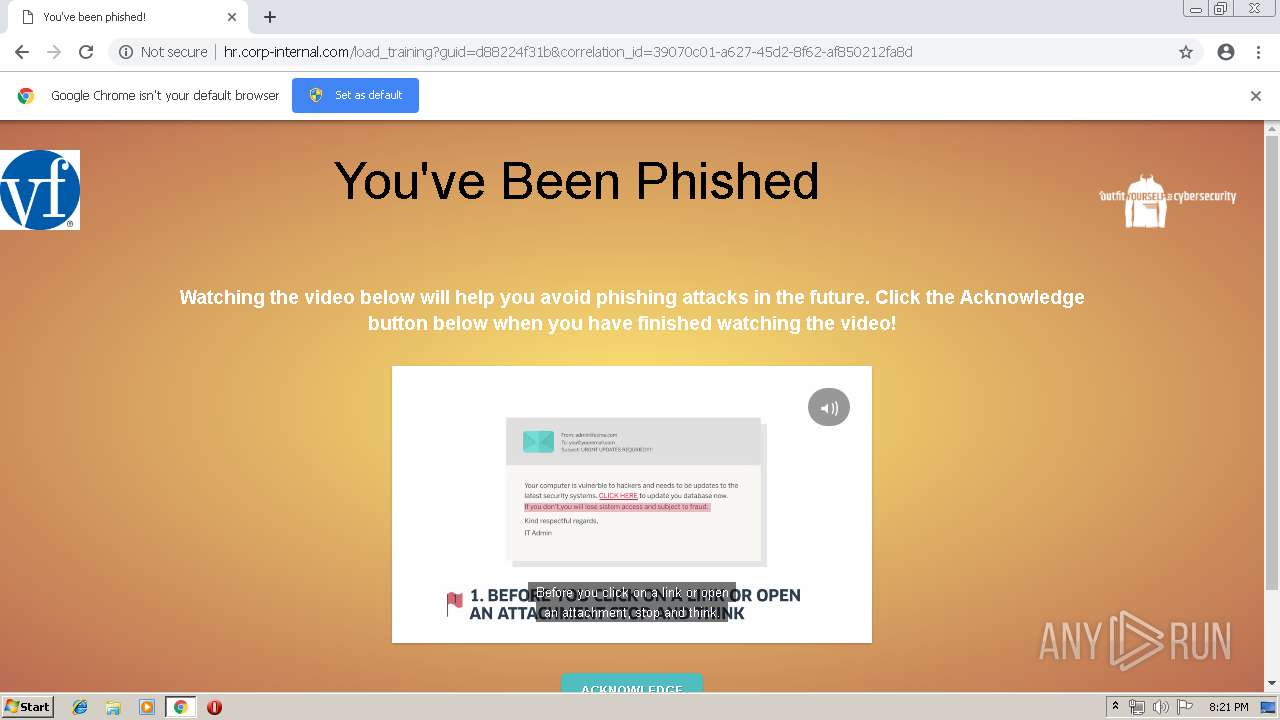
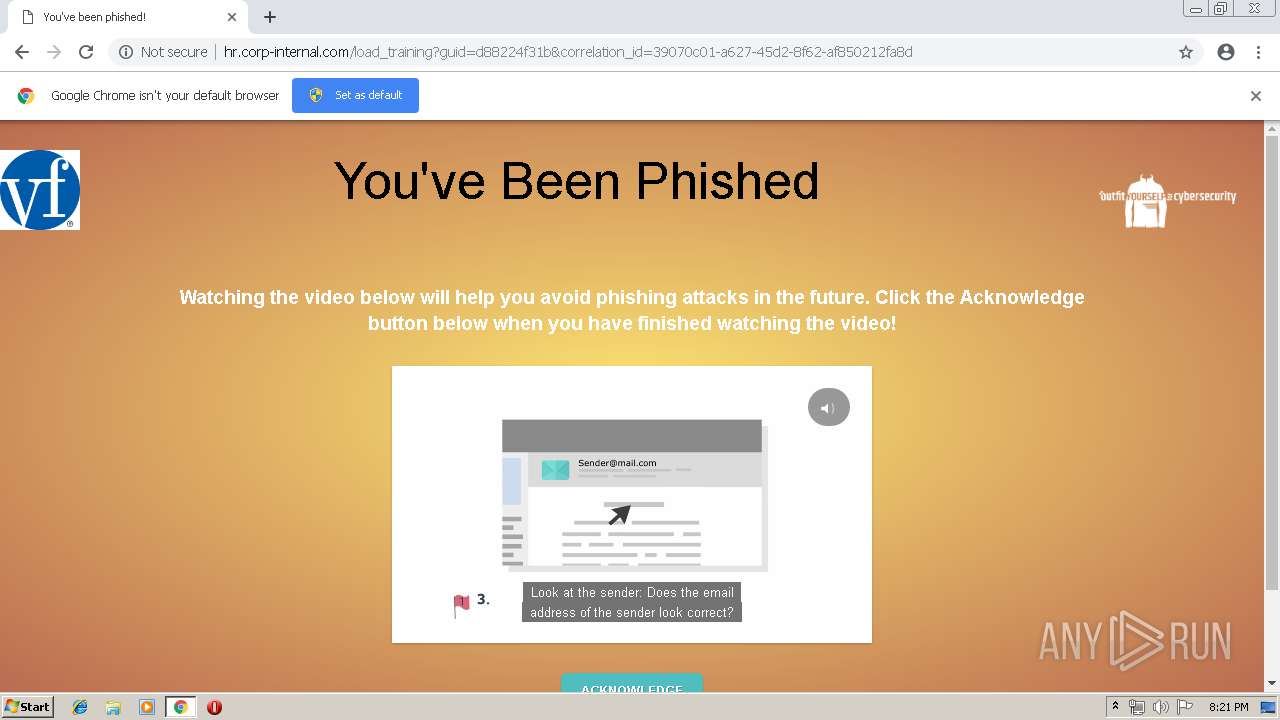
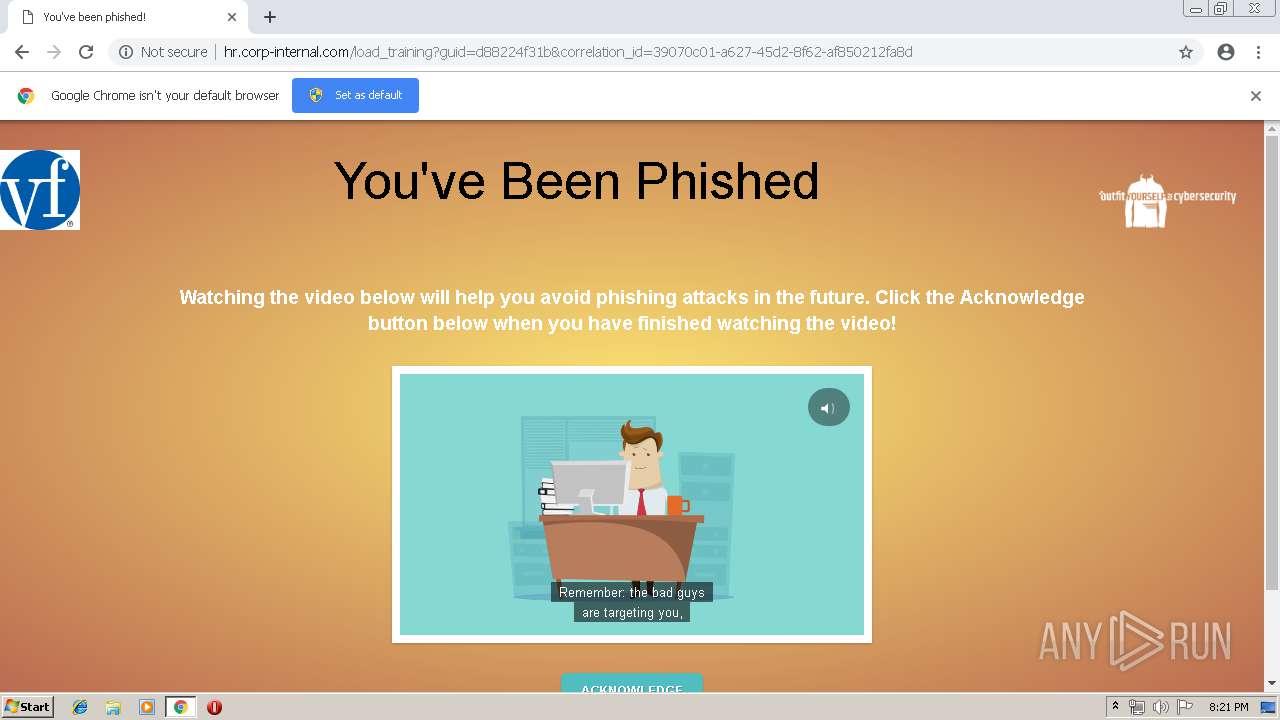
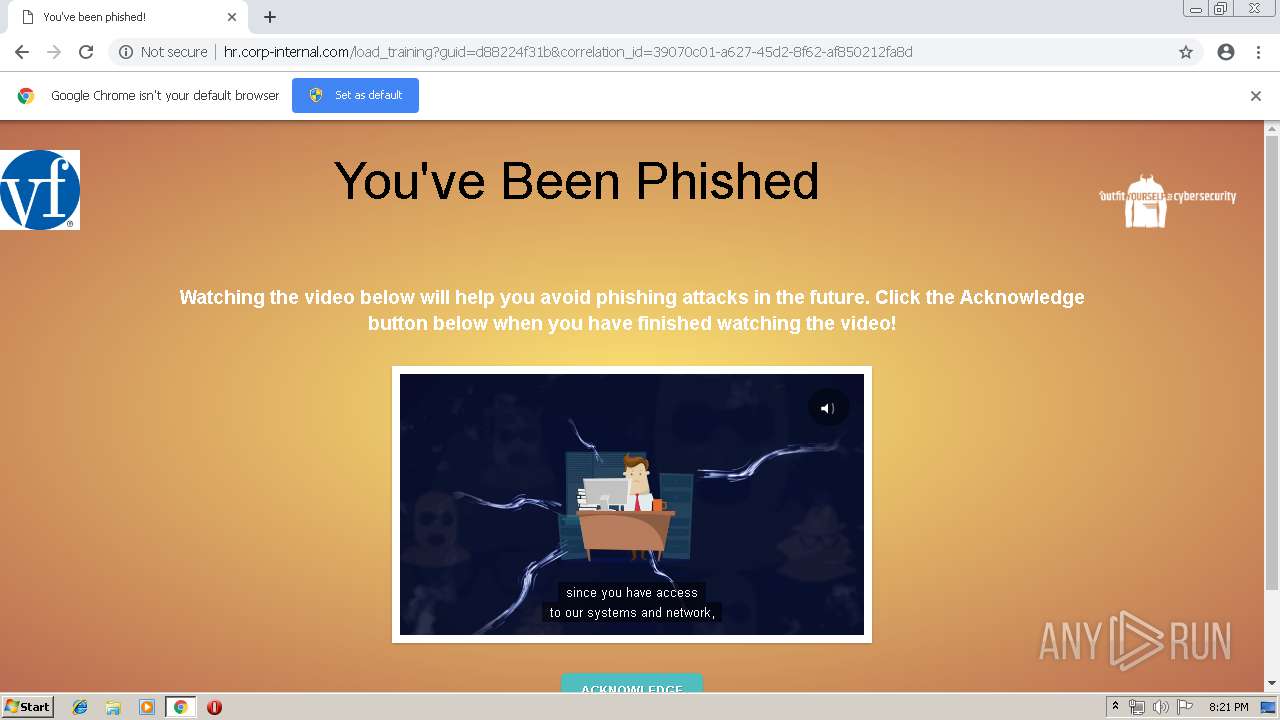
| URL: | http://HR.corp-internal.com/d88224f31b?l=7 |
| Full analysis: | https://app.any.run/tasks/979b3509-1828-45f6-8e65-8ad267ddc661 |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2019, 19:20:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 550BB9FD3F5FB086D9AD19FD854319D9 |
| SHA1: | 04D4B5E8F67D29E6517FED84053497583B7E0E2F |
| SHA256: | C5673915100C2F131138C9664A91A3098293920495251616DEAA055AD076A493 |
| SSDEEP: | 3:N1K0FGTadVXRDG/n:C0FKcXk |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3888)
INFO
Application launched itself
- chrome.exe (PID: 3888)
Reads settings of System Certificates
- chrome.exe (PID: 3888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
16
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://HR.corp-internal.com/d88224f31b?l=7 | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 73.0.3683.75 | ||||
| 3392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f3c0f18,0x6f3c0f28,0x6f3c0f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 73.0.3683.75 | ||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3924 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Version: 73.0.3683.75 | ||||
| 2756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17152363334188467644 --mojo-platform-channel-handle=956 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Version: 73.0.3683.75 | ||||
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --service-pipe-token=5326717142619875758 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5326717142619875758 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 2432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --service-pipe-token=8154669110630229551 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8154669110630229551 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Version: 73.0.3683.75 | ||||
| 1412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --service-pipe-token=14404017145720924772 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14404017145720924772 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2124 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 3680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9480457502858544896 --mojo-platform-channel-handle=3624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
| 536 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=16793263543806785143 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16793263543806785143 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Version: 73.0.3683.75 | ||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=940,7684098884706590447,18307735252959577817,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9036744120946576334 --mojo-platform-channel-handle=4568 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 | ||||
Total events
573
Read events
486
Write events
82
Delete events
5
Modification events
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2140) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3888-13200434441105625 |
Value: 259 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
73
Text files
127
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cc896bef-a39f-4403-a329-e075036bb8df.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
74
TCP/UDP connections
52
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | chrome.exe | GET | 200 | 52.202.226.7:80 | http://hr.corp-internal.com/assets/google-tracking.js?guid=d88224f31b&correlation_id=39070c01-a627-45d2-8f62-af850212fa8d | US | text | 316 b | suspicious |
3888 | chrome.exe | GET | 200 | 52.202.226.7:80 | http://hr.corp-internal.com/d88224f31b?l=7 | US | html | 927 b | suspicious |
3888 | chrome.exe | GET | 200 | 151.101.2.110:80 | http://fast.wistia.com/embed/medias/p2ig2icx0p.json?callback=wistiajson1 | US | text | 16.1 Kb | whitelisted |
3888 | chrome.exe | GET | 200 | 52.202.226.7:80 | http://hr.corp-internal.com/assets/google-tracking.js?g=d88224f31b | US | text | 316 b | suspicious |
3888 | chrome.exe | GET | 200 | 52.85.182.89:80 | http://d2wy8f7a9ursnm.cloudfront.net/bugsnag-2.min.js | US | text | 2.89 Kb | shared |
3888 | chrome.exe | GET | 200 | 172.217.22.42:80 | http://ajax.googleapis.com/ajax/libs/jquery/2.1.4/jquery.min.js | US | text | 29.0 Kb | whitelisted |
3888 | chrome.exe | GET | 200 | 52.202.226.7:80 | http://hr.corp-internal.com/trace?id=undefined&msg=window.tracking_id%20is%20not%20set%2C%20let%27s%20get%20it&correlation_id=39070c01-a627-45d2-8f62-af850212fa8d | US | binary | 20 b | suspicious |
3888 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAKXB1YM1Knrv%2BJy8eCW2II%3D | US | der | 471 b | whitelisted |
3888 | chrome.exe | GET | 200 | 52.202.226.7:80 | http://hr.corp-internal.com/assets/all.js?g=d88224f31b | US | text | 6.98 Kb | suspicious |
3888 | chrome.exe | GET | 200 | 52.202.226.7:49152 | http://hr.corp-internal.com:49152/alt_pixel_click_d88224f31b.gif?correlation_id=39070c01-a627-45d2-8f62-af850212fa8d | US | binary | 20 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | chrome.exe | 52.202.226.7:80 | hr.corp-internal.com | Amazon.com, Inc. | US | unknown |
3888 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
— | — | 52.202.226.7:49152 | hr.corp-internal.com | Amazon.com, Inc. | US | unknown |
3888 | chrome.exe | 172.217.22.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 216.58.210.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 52.216.21.179:443 | tslp.s3.amazonaws.com | Amazon.com, Inc. | US | shared |
— | — | 172.217.22.42:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 52.202.226.7:443 | hr.corp-internal.com | Amazon.com, Inc. | US | unknown |
3888 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3888 | chrome.exe | 23.40.0.154:443 | java.com | Akamai Technologies, Inc. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hr.corp-internal.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
tslp.s3.amazonaws.com |
| shared |
java.com |
| whitelisted |
d2wy8f7a9ursnm.cloudfront.net |
| shared |
ajax.googleapis.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dataentry.threatsim.com |
| suspicious |
www.google-analytics.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3888 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3888 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |